计算机病毒可按照多种方式进行分类,嵌入式病毒是根据()进行分类的一类病毒。 攻击对象的机型。 按攻击计算机的操作系统。 按照计算机病毒的链接方式分类。 按计算机病毒的传染方式。
You are the network administrator for your company. The network consists of a single Active Directory domain. All network servers run Windows Server 2003. A server named Server54 hosts all shared documents for the legal and human resources departments. Server54 is frequently accessed and updated throughout the business day. Users report extremely slow response times when they try to open the shared documents. You log on to Server54 and observe real-time data indicating that the processor is operating at 100 percent of capacity. Now you need to gather additional data to diagnose the cause of the problem. What should you do? () In System Monitor, create an alert that will be triggered when processor usage exceeds 80 percent for more than five minutes.。 In Event Viewer, open and review the application log for System Monitor events.。 In Task Manager, review the Processes tab to see the percentage of processor capacity used by each application.。 In the Performance console, create a counter log to track processor usage.。
SQL Server的数据库分为()和()两种类型。
具有探索倾向的人,适合下列哪些职业()。 法庭速记员。 科研人员。 地质学者。 机械制图员。
护法运动
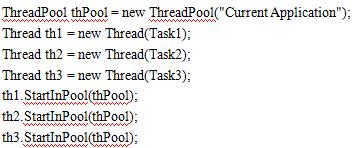
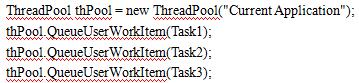
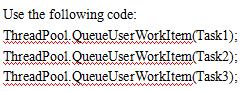
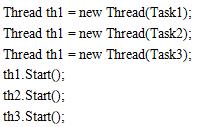
您目前正在开发一种业务逻辑组件,需要长时间的计算过程中。
您已经确定在该应用程序,可以以异步方式进行的许多任务。
你注意到这些任务相互依赖,并需要复杂的同步技术,因此,它可以有效地管理。
您决定使用 Microsoft.ET 2.0,利用其新的线程管理功能。
您需要创建和启动应用程序线程。
你应该做什么?()